It’s great to allow employees to work from home using any device, but any time you give someone the ability to access your network, you make your business vulnerable to hackers and thieves who can sabotage your network and/or steal valuable data.
We specialise in providing remote IT solutions that allow your users to work anywhere at any time, on any device.
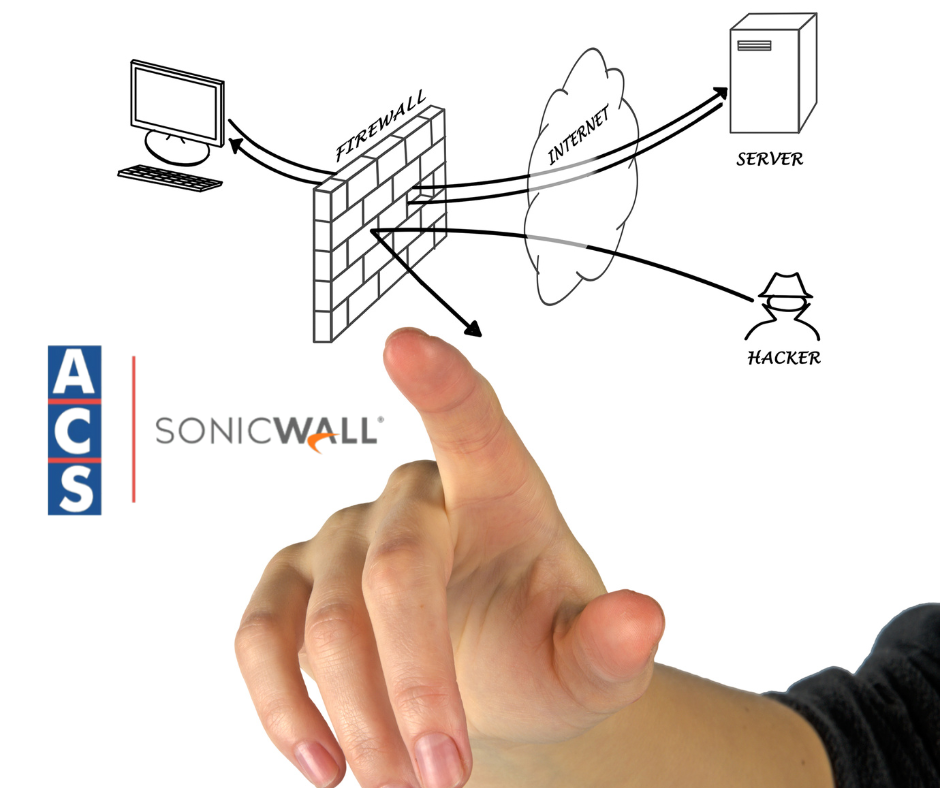
Every business needs to have a process to protect its network from breaches and threats while providing the remote access that modern business demands.
What is Secure Remote Access?
In today’s rapidly changing world, the business environment requires that your employees and vendors have access to your company’s network and applications regardless of where they are or what device they are using. Doing so makes it possible for them to complete crucial tasks while maintaining their work-life balance. More and more business is conducted in the cloud from remote locations, including tech support, e-commerce, record storage, and other routine business functions.
Secure remote access software provides the tools to ensure that anyone who accesses your network is authenticated and uses a secure connection.
How Will Secure Remote Access Solutions Benefit My Business?
Enabling secure remote access at your organization can deliver big benefits such as:
- Increased productivity – users can access files outside the office
- Reduced risk – you determine authorized users and their access level
- Reduced overhead expenses – reduces office space requirements and energy costs
- Improved work-life balance – flexible work scheduling
Getting Started with Secure Remote Access.
When evaluating a secure remote access solution for your business, it’s important to:
- Ensure that your remote access design matches your security policy
- Protect the network from theft and leakage of sensitive data
- Assess traffic demands to ensure adequate support to the needs of remote workers
Remote Access Solution for your business?
ACS is ready to assist you with every phase of choosing and leveraging the right solution for your IT environment. Our approach includes:
- An initial discovery session to understand your goals, requirements, and budget
- An assessment review of your existing environment and definition of project requirements
- Detailed vendor evaluations, recommendations, future design and proof of concept
- Procurement, configuration, and deployment of the final solution
- Ongoing product lifecycle support